Prevention
We take your security to the next level with clarity and structure.
Protect your data!
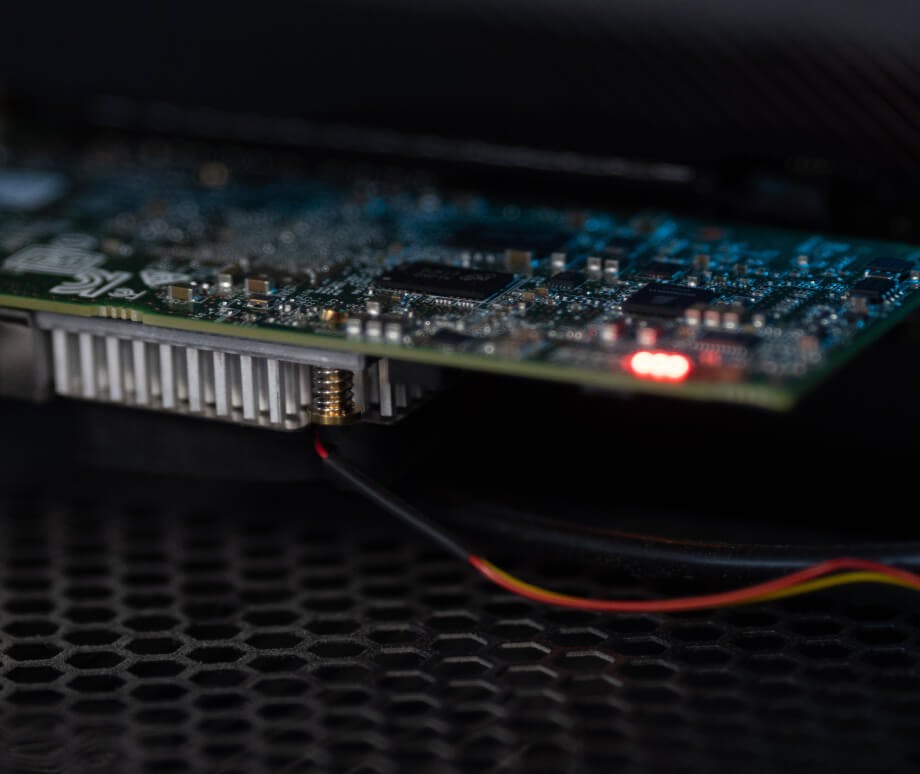
Defense against cyber attacks starts with proactive elimination of vulnerabilities in your IT infrastructure and careful handling of your data.
IT Security
We empower you to navigate the evolving landscape of security threats.
Our IT security assessment offers a comprehensive analysis of your organization's information and cybersecurity infrastructure, serving as a foundational tool for effective risk management. The objective is to pinpoint and mitigate security vulnerabilities while seamlessly integrating best-practice standards. Upon completing the assessment, you will gain insights into dependencies with internal and external IT stakeholders, identify critical information requiring protection, pinpoint areas of vulnerability, and establish actionable steps for improvement.
We adhere to internationally recognized standards such as ISO/IEC 2700x and comply with the IT baseline protection catalogs of the German Federal Office for Information Security (BSI).
Incident Response Retainer
A cyber attack can hit your company at any time. We prepare you for the worst case scenario.
Given the current threat landscape, the likelihood of a security breach affecting your company is significant. Therefore, it is crucial to be prepared for a cyber attack scenario and to have the ability to respond swiftly and effectively, with professional assistance.
Our Incident Response Retainer service is specifically designed for enterprises, focusing precisely on this kind of preparedness. Through interactive workshops, we simulate potential attack scenarios and train you on the correct response protocols. Our support is available around the clock to assist you in the event of a cyber incident.

Data Management
We digitize and organize your data, restore lost data or delete it permanently.
Our Data Management solutions encompass a comprehensive suite of services — from document scanning, preparation, sorting, and indexing to secure archiving. In collaboration with you, we either integrate with your existing archiving structures or enhance them for optimal efficiency. Our expertise extends to the recovery and secure erasure of deleted data, as well as the responsible disposal of related data storage devices.
It's worth noting that pre-owned devices often contain retrievable data, which can include sensitive personal information. We take stringent measures to ensure that confidential data is not compromised, safeguarding it from unauthorized access.


